EVERY website is being hacked. And we do mean EVERY website! Now to be fair we can’t make that claim with absolute proof which would mean looking at the data on every website and show the evidence of the hacking attempt. But we are making what we believe is a very reasonable extrapolation. In almost a decade of managing a multitude of websites, we’ve yet to see one that wasn’t probed by a hacker in some way or other.
Here’s an example of a log from this morning as I wrote this post!

536 different hosts attempted login into this one particular site!
When I say to our various clients that EVERY website is being probed by hackers they look at me rather incredulously and think I am exaggerating. I am not. Sometimes I show clients my website admin console and asked them to pick a site at random. We then log into that site and look at the log files and we will see things like this:
This screenshot shows a few examples of how hackers try to login. One is by trying to use the user ID “admin” which is the default WordPress user ID. Since they know what is normally a valid administrative account user name, the hackers try various passwords with that ID. However, in our case, we disable the user ID ‘admin’ and automatically lock out anyone who attempts to login with that ID.
The hackers can also figure out other user ID’s. You can see one of these in the screen shot: justcallmebilly
We really can’t prevent hackers from figuring out valid user names but we have other ways to circumvent this particular approach from working.
Sometimes we look at the IP addresses to see where these hacking attempts are coming from but often the hackers are using VPNs which makes it appear they are coming from a different physical location. That’s the case with the first two IPs in the list which are US based. The third one however is from the Netherlands.
After seeing these things, clients are generally on board with my statement that every website is being hacked but often ask the follow-up question “Why do they care about my little site here in ….”.
My answer is that they don’t. They don’t know who you are and don’t care. And that’s where we get into how this actually works. People think of a website being hacked as some guy in a dark basement typing away on a keyboard. But in reality, the vast bulk of hacking attempts are done by bots. These are computer scripts that grab website addresses from publicly available information and then the software program runs the script against that URL attempting to get inside the website. This can be done by attempted logins and other ways. Realize that there are more ways into a house than just through the locked front or back door.
Once clients understand this, the next question they invariably ask is “What do they want? I don’t have anything on my website of value!”
Well…yes you do! For one thing, you have computing resources. If a hacker can get control of your website he can use that to launch attacks on other websites. And you will look like the bad guy!
It’s estimated, by the way, that there are hundreds of millions of computers involved in hacking attempts worldwide.
According to Purplesec cybercrime is up more than 600% during the CoVid pandemic. This article provides a wide-range of hair-raising statistics about cyber crime. We’ll share just a few to get your attention:
- 92% of malware is delivered by email
- 98% of mobile malware targets are Android devices
- Over the lat year MacOS malware has increased by 165%
- 7 out of every 10 malware payloads were ransomware
- It’s estimated that 230,000 new malware samples are produced EVERY DAY
- Over 18 MILLION websites are infected with malware at a given time each week
- 1.5 Million new phishing sites are created each month.
This article says that in an analysis of nearly 4000 confirmed security breaches over half were a result of hacking attempts, followed by phishing which accounted for 33%. The third largest culprit was malware accounting for 28%. The article also says that 99.9% of accounts get hacked for one reason only – not using mult-factor authentication.
This article is one of many that explains why hackers hack.
The number one motivation is financial gain. This can include various identity theft related crimes such as:
- Stealing money from your bank account
- Taking out loans in your name
- Opening a credit card in your name and using it
- Creating fake social accounts in your name in efforts to scam other people
- Selling data on the dark web
- Blackmailing victims with information gleaned
- Selling malware
Beyond financial gain there are a variety of other reasons hacking occurs. This includes various political agendas, corporate espionage, personal revenge, causing harm for enjoyment, proving hacking capability (Facebook is often a target in this regard) and other less obvious reasons.
Knowing all this, what can individuals do to keep their data safe?
1. Use a password manager
Using a password manager that can create long (35 characters or more) passwords that are only used once means user will avoid a few issues that people who don’t use password managers face:
a. Reusing passwords – this is bad practice because if you get compromised on one site, you run more risk of being compromised on other sites.
b. Using short passwords because you are manually typing them in or they are easier to remember – again, another bad practice – short passwords are hacked much easier than long ones as there are far less combinations of the characters. And if you can remember the password chances are it’s a simple password that doesn’t have a combination of upper and lower case, numbers and symbols.
c. Malware programs such as keyloggers if present on a user’s computer can capture passwords typed in and transfer them to the hacker using the user’s computer resources.
Again, using a password manager avoids these issues. And in practice, as a bonus, you will find it’s actually much more efficient! i.e. it’s faster as you are auto-populating your user name and password.
2. Use multi-factor authentication.
This either involves having a code sent to your email (which hopefully is not compromised!) or using a code generator. With the code generators a new code (generally six digits) is generated every 30 seconds. You must enter the correct code within the time limit or wait for the next code. Another way is to have a code sent by SMS message (but this is viewed as less secure than using a code generator program). Another way, less common but very secure is to use a hardware key such as Yubikey or Nitrokey. This article covers this in more detail.
3. Be careful with links and attachments in emails.
You can verify links and attachments using Virus Total.
4. Use anti-virus software on your computer.
This includes Macs! While Apple devices are less prone to viruses and other malware they are most definitely not immune to them.
5. Back-up any data you don’t want to lose. And then back it up again.
This advice which applies to individuals also applies to websites.
Unleashing the Power of Google Analytics 4 (GA4) – The Future of Web Analytics
Introduction: Having an online analytics platform is very important for all businesses that have any kind of online presence (and, of course, that’s almost every business!). The first version of Google Analytics was introduced in November 2005. In October 2020, Google introduced the latest version, called Google Analytics 4 (commonly known as GA4) which gives a detailed insight to all the businesses that have their website properly connected to GA4, including such insights as user engagement on the website, number of impressions, click-through rate, conversion rate, and much more. ...
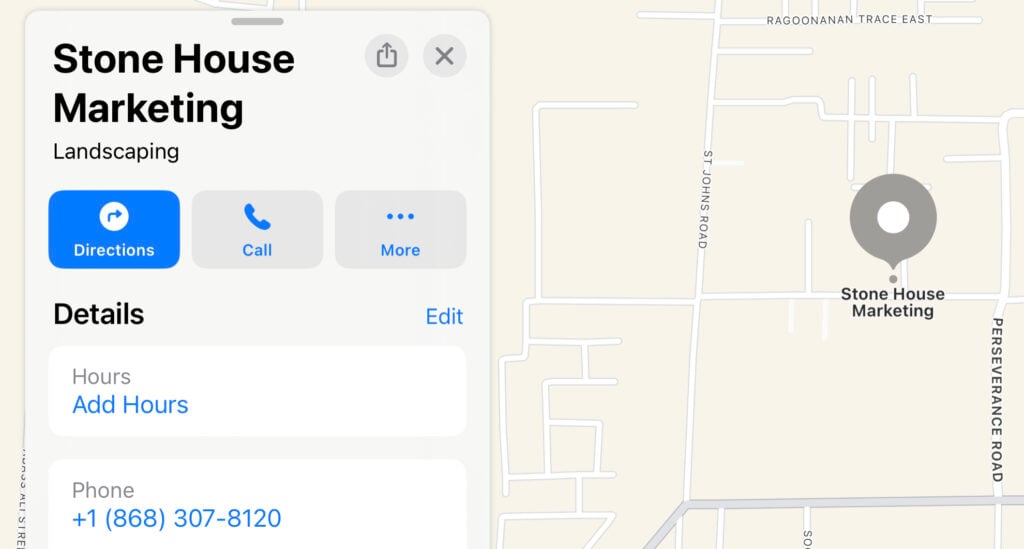
Mastering Apple Maps SEO: Your Key to Dominating Local Search and Boosting Business Visibility!
A mapping software application called Apple Maps is pre-installed on all Apple devices. Many businesses are well aware of the importance of having a Google Business Place (formally known as Google My Business) listing so that their business shows up in the local Google search listings. Less known though is doing a listing to show up on Apple Maps! Due to Apple’s enormous user base, this is a massive, largely untapped opportunity for businesses to rank in search! Key fundamentals of Apple Maps include: 1] Apple Maps Indoor Navigation Function: This function is particularly helpful for...
The Future of SEO: Voice Search Optimization
Hello, digital entrepreneurs! In the current scenario, technology is constantly evolving, and it is crucial for us to utilize these technological changes and take advantage of these new technologies as rapidly as possible. Therefore, in today's blog you'll learn how digital assistants like Siri, Google Assistant, and Alexa are facilitating customer and business connections. 1) The growth of voice search: According to recent studies, voice search engines produce $40 billion in annual revenue, indicating that the need for voice help is already rising rapidly. And people are utilizing these...
New Website Design Quinte Hills Golf
StoneHouseMarketing Solutions, Inc is pleased to release our newest website design, Quinte Hills Golf Course, complete with a dynamic header, eye-catching background photos, and a mobile menu that is easy to use. You can see it here. The site features an interesting home page main header comprised of five section. When you move your mouse over a different section, the background image will change to display a different golf course hole. It's a great way to showcase the golf course! We also added a weather widget on the home page so that golfers will know what the local weather is at...
Mac OS ToolBar on All Screens
How to put your Mac OS toolbar and dock on EVERY screen in a multi-monitor setup
Best SEO Practices According to ChatGPT
I asked the AI program ChatGPT the following:Research the top Search Engine Optimization practices for 2023 and include references. Here's what it came back with! I'm sorry, but I am not able to browse the web, so I cannot research current SEO practices for you. However, I can tell you about some general SEO best practices that have remained consistent over the years and are likely to continue to be effective in the future. These include: 1. Make sure your website is mobile-friendly and loads quickly.2. Use descriptive, keyword-rich title tags and meta descriptions to help search engines...
Fastest Website Hosting Service
For the fastest hosting service you can get for small and medium sized businesses, it's really quite simple! We recommend hosting with us! The screen shot you see above shows you our website speed the day this article was written. We used GTMetrix to test our home page and you can do the same with your website. Just go to GTMetrix.com and type in your website address starting with https:// Note: There is another website tool you can use that will scan EVERY page of your website simply by entering your site address. This one, by a company called Experte, is available here. Why is this kind...
LastPass Phishing Email
IF YOU USE LASTPASS, PLEASE READ THIS EMAIL! Even if you don't use LastPass, there are valuable lessons here in this article on online security that might potentially save you untold grief in the future. Over the weekend I received an email that could have cost me the keys to the kingdom. By that, I mean giving a hacker every password I have! And I have literally hundreds of different passwords. Here's the email I received:On the surface this looks pretty legit! It says it's coming from Lastpass. But when I click on the name "Lastpass" I see that the underlying email address is...
The Most Important Thing for Local SEO
What is the most important thing for local SEO? The most important thing for local SEO is Google My Business (GMB). And yet, most local businesses we deal with seem much more focused on various social media networks such as Facebook, Instagram, Pinterest (which is great for certain market segments – bridal shops come to mind), and other ones such as Twitter, Linked In and so on. They generally don’t pay much attention to Google My Business. This is, in our opinion, a huge mistake. We’re not saying those other networks aren’t helpful for drumming up or building business, but in terms of...
The ROI of SEO
Let's look at the ROI of SEO i.e. the return on investment of spending money on SEO. As a business owner you may have thought about investing in Search Engine Optimization, or SEO for short, but weren’t sure if it really made good business sense. This post can help you determine whether SEO is a worthwhile investment or not. The answer ranges from “absolutely not” to “absolutely”! It really depends upon on several different things. For example, we recently talked to a dentist about marketing, and he told us that he is fully booked and not taking on any clients! Well, then. He clearly...